As part of my journey with Node.js I decided I wanted to see exactly what was happening on the wire. I decided to use Burp Suite as the Http proxy interceptor and Wireshark as the network sniffer (not an interceptor). Wireshark can’t alter the traffic, it can’t decrypt SSL traffic unless the encryption key can be provided and Wireshark is compiled against GnuTLS.
This post is targeted at getting Wireshark running on Linux. If you’re a windows user, you can check out the Windows notes here.
When you first install Wireshark and try to start capturing packets, you will probably notice the error “You didn’t specify an interface on which to capture packets.”
When you try to specify an interface from which to capture, you will probably notice the error “There are no interfaces on which a capture can be done.”
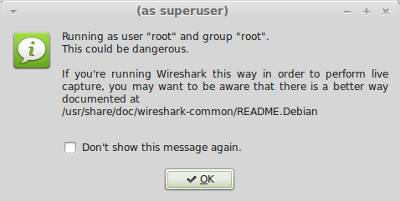
You can try running Wireshark as root: gksudo wireshark
This will work, but of course it’s not a good idea to run a comprehensive tool like Wireshark (over 1’500’000 lines of code) as root.
So what’s actually happening here?
We have dumpcap and we have wireshark. dumpcap is the executable responsible for the low level data capture of your network interface. wireshark uses dumpcap. Dumpcap needs to run as root, wireshark does not need to run as root because it has Privilege Separation.
If you look at the above suggested “better way” here, this will make a “little” more sense. In order for it to make quite a lot more sense, I’ll share what I’ve just learnt.
Wireshark has implemented Privilege Separation which means that the Wireshark GUI (or the tshark CLI) can run as a normal user while the dumpcap capture utility runs as root. Why can’t this just work out of the box? Well there is a discussion here on that. It doesn’t appear to be resolved yet. Personally I don’t think that anybody wanting to use wireshark should have to learn all these intricacies to “just use it”. As the speed of development gets faster, we just don’t have time to learn everything. Although on the other hand, a little understanding of what’s actually happening under the covers can help in more ways than one. Anyway, enough ranting.
How do we get this to all “just work”
from your console:
sudo dpkg-reconfigure wireshark-common
You’ll be prompted:
Respond yes.
The wireshark group will be added
If the Linux Filesystem Capabilities are not present at the time of installing wireshark-common (Debian GNU/kFreeBSD, Debian GNU/Hurd), the installer will fall back to set the set-user-id bit to allow non-root users to capture packets. Custom built kernels may lack Linux Capabilities.
The help text also warns about a security risk which isn’t an issue because setuid isn’t used. Rather what actually happens is the following:
addgroup --quiet --system wireshark chown root:wireshark /usr/bin/dumpcap setcap cap_net_raw,cap_net_admin=eip /usr/bin/dumpcap
You will then have to manually add your user to the wireshark group.
sudo adduser kim wireshark # replacing kim with your user
or
usermod -a -G wireshark kim # replacing kim with your user
log out then back in again.
I wanted to make sure that what I thought was happening was actually happening. You’ll notice that if you run the following before and after the reconfigure:
ls -liah /usr/bin/dumpcap | less
You’ll see:
-rwxr-xr-x root root /usr/bin/dumpcap initially
-rwxr-xr-x root wireshark /usr/bin/dumpcap after
And a before and after of my users and groups I ran:
cat /etc/passwd | cut -d: -f1 cat /etc/group | cut -d: -f1
–
Alternatively to using the following as shown above, which gives us a nice abstraction (if that’s what you like):
sudo dpkg-reconfigure wireshark-common
We could just run the following:
addgroup wireshark sudo chgrp wireshark /usr/bin/dumpcap sudo chmod 750 /usr/bin/dumpcap sudo setcap cap_net_raw,cap_net_admin+eip /usr/bin/dumpcap
The following will confirm the capabilities you just set.
getcap /usr/bin/dumpcap
What’s with the setcap?
For full details, run:
man setcap man capabilities
setcap sets the capabilities of each specified filename to the capabilities specified (thank you man ;-))
For sniffing we need two of the capabilities listed in the capabilities man page.
- CAP_NET_ADMIN Perform various network-related operations (e.g., setting privileged socket options, enabling multicasting, interface configuration, modifying routing tables). This allows dumpcap to set interfaces to promiscuous mode.
- CAP_NET_RAW Use RAW and PACKET sockets. Gives dumpcap raw access to an interface.
For further details check out Jeremy Stretch’s explanation on Linux Filesystem Capabilities and using setcap. There’s also some more info covering the “eip” in point 2 here and the following section.
man capabilities | grep -A24 "File Capabilities"
Lets run Wireshark as our usual low privilege user
Now that you’ve done the above steps including the log off/on, you should be able to run wireshark as your usual user and configure your listening interfaces and start capturing packets.
Also before we forget… Ensure Wireshark works only from root and from a user in the “wireshark” group. You can add a temp user (command shown above).
Log in as them and try running wireshark. You should have the same issues as you had initially. Remove the tempuser:
userdel -r tempuser
Tags: node, Node.js, packet sniffing, wireshark

April 21, 2013 at 02:05 |
Thanks for sharing.
Stretch at PacketLife has a similar post [0]
[0] http://packetlife.net/blog/2010/mar/19/sniffing-wireshark-non-root-user/