The following is the process I found to set-up the pass-through of the very common USB TP-LINK TL-WN722N Wifi adapter (which is known to work well with Linux) to a Virtual Host Kali Linux 1.1.0 (same process for 2.0) guest, by-passing the Linux Mint 17.1 (Rebecca) Host.
Virtualisation
VirtualBox 4.3.18_r96516
Wifi adapter
TP-LINK TL-WN722N Version 1.10
- chip-set: Atheros ar9271
- Vendor ID: 0cf3
- Product ID: 9271
- Module (driver): ath9k_htc
Useful commands
iwconfigifconfigsudo lshw -C networkiwlist scanlsusbdmesg | grep -e wlan -e ath9- contents of
/var/log/syslog lsmod- Release DHCP assigned IP. Similar to Windows ipconfig /release
dhclient -r [interface-name] - Renew DHCP assigned IP. Similar to Windows ipconfig /renew
dhclient [interface-name]
Why?
I want to be able to access the internet on my laptop at the same time that I’m penetration testing a client network. I use my phone as a wireless hot-spot to access the internet. The easiest way to do this is to use the laptops on-board wireless interface to connect to the phones wireless hot-spot and pass the USB Wifi adapter straight to the guest.
Taking the following statement: “The preferred way to get Internet over wlan into a VM is to use the WLAN adapter on the host and using normal NAT for the VM. Passing USB WLAN adapters to the guest is almost untested.” from here, I like to think of more of a challenge than anything else. It can be however, something to keep in mind. if you’re prepared to persevere, you’ll get it working.
How
Reconnaissance
When you plug the Wifi adapter into your laptop and run lsusb, you should see a line that looks like:
ID 0cf3:9271 Atheros Communications, Inc. AR9271 802.11n
The first four hex digits are the Vendor ID and the second four hex digits are the Product ID.
If you have a look from the bottom up of the /var/log/syslog file, you’ll see similar output to the following:
kernel: [ 98.212097] usb 2-2: USB disconnect, device number 3 kernel: [ 102.654780] usb 1-1: new high-speed USB device number 2 using ehci_hcd kernel: [ 103.279004] usb 1-1: New USB device found, idVendor=0cf3, idProduct=7015 kernel: [ 103.279014] usb 1-1: New USB device strings: Mfr=16, Product=32, SerialNumber=48 kernel: [ 103.279020] usb 1-1: Product: UB95 kernel: [ 103.279025] usb 1-1: Manufacturer: ATHEROS kernel: [ 103.279030] usb 1-1: SerialNumber: 12345 kernel: [ 103.597849] usb 1-1: ath9k_htc: Transferred FW: htc_7010.fw, size: 72992 kernel: [ 104.596310] ath9k_htc 1-1:1.0: ath9k_htc: Target is unresponsive kernel: [ 104.596328] Failed to initialize the device kernel: [ 104.605694] ath9k_htc: probe of 1-1:1.0 failed with error -22
Provide USB privileges to guest
First of all you need to add the user that controls guest to the vboxusers group on the host so that VM’s can control USB devices. logout/in of/to host.
Provide USB recognition to guest
Install the particular VirtualBox Extension Pack on to the host as discussed here. These packs can be found here. If you have an older version of VirtualBox, you can find them here. Don’t forget to checksum the pack before you add the extension.
apt-get updateapt-get upgradeapt-get dist-upgradeapt-get install linux-headers-$(uname -r)- Shutdown Linux guest OS
- Apply extension to VirtualBox in the host at: File -> Preferences -> Extensions
Blacklist Wifi Module on Host
Unload the ath9k_htc module to take effect immediately and blacklist it so that it doesn’t load on boot. The module needs to be blacklisted on the host in order for the guest to be able to load it. Now we need to check to see if the module is loaded on the host with the following command:
lsmod | grep -e ath
We’re looking for ath9k_htc. If it is visible in the output produced from previous command, unload it with the following command:
modprobe -r ath9k_htc
Now you’ll need to create a blacklist file in /etc/modprobe.d/. Create /etc/modprobe.d/blacklist-ath9k.conf and add the following text into it and save:
blacklist ath9k_htc
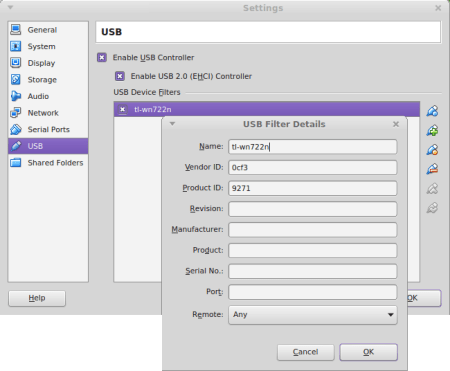
Now go into the settings of your VM -> USB -> and add a Device Filter. I name this tl-wn722n and add the Vendor and Product ID’s we discovered with lsusb. Make sure The “Enable USB 2.0 (EHCI) Controller” is enabled also.
Upgrade Driver on Guest
Start the VM.
Install the latest firmware-atheros package
On the guest, check to see which version of firmware-atheros is installed:
dpkg-query -l '*atheros*'
Will probably be 0.44kali whether you’re on Kali Linux 1.0.0 or 2.
aptitude show firmware-atheros
Will provide lots more information if you’re interested. So now we need to remove this old package:
apt-get remove --purge firmware-atheros
Add the jessie-backports (that’s Debian 8.0) repository to your /etc/apt/sources.list in the following form:
deb http://ftp.nz.debian.org/debian jessie-backports main contrib non-free
Change the country prefix to your country if you like and follow it up with an update:
apt-get update
Then install the later package from the new repository we just added:
apt-get install -t jessie-backports firmware-atheros
Now if you run the dpkg-query -l '*atheros*' command again, you’re package should be on version 0.44~bp8+1
Test
Plug your Wifi adapter into your laptop.
In the Devices menu of your guest -> USB Devices, you should be able to select the “ATHEROS USB2.0 WLAN” adapter.
Run dmesg | grep htc and you should see something similar to the following printed:
[ 4.648701] usb 2-1: ath9k_htc: Firmware htc_9271.fw requested [ 4.648805] usbcore: registered new interface driver ath9k_htc [ 4.649951] usb 2-1: firmware: direct-loading firmware htc_9271.fw [ 4.966479] usb 2-1: ath9k_htc: Transferred FW: htc_9271.fw, size: 50980 [ 5.217395] ath9k_htc 2-1:1.0: ath9k_htc: HTC initialized with 33 credits [ 5.860808] ath9k_htc 2-1:1.0: ath9k_htc: FW Version: 1.3
You should now be able to select the phones wireless hot-spot you want to connect to in network manager.
Additional Resources
- ath9k_htc Debian Module
- VirtualBox information around setting up the TL-WN722N
- TP-LINK TL-WN722N wiki
- Loading and unloading Linux Kernel Modules
- Kernel Module Blacklisting